If you’ve been following along, you see how Cloudy brought together a strong understanding of identity, phishing-resistant authentication, good rules for authorizing people and groups, and checks on device health — all to make sure the cloud environment, with its software, data and processes, is safe for employees and end users.
Want to go back and refresh your memory? See the whole series at gcpcomics.com
Use your understanding about your systems, services and applications to set policies that make sense for your specific set of risks and goals.
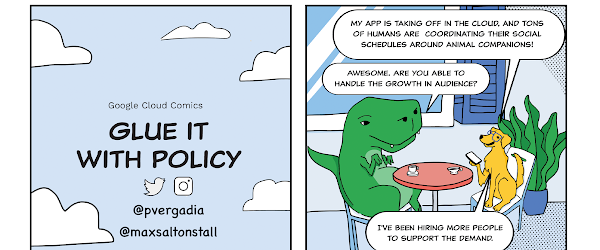
In this issue you can see how, and why, Cloudy and Dino pull it all together.
This process of defining rules and policies involves collaboration between security and identity teams, application owners, compliance and other internal groups.
Setting up the right policies means deciding exactly how and when people earn the appropriate levels of trust that your organization establishes for accessing internal services and corporate resources like SaaS applications. A framework for levels of trust can actually be pretty simple. For example:
High: The most trusted, in line with all security policies and recommendations, and able to access the most secure servicesMedium: Limited trust when out of compliance for some policies.Low: Useful for devices that are in the inventory but not properly set up, or have had issues and need remediationNone: The default state for any unknown or unrecognized device
We want to keep things as simple as possible, without diluting them to be overly simplistic. So if you need more granular policies, or have specific regulatory requirements around roles, data stores or offices, you always have the flexibility to customize policies to suit your needs.
Increase the security posture of your organization by implementing a modern security model to help ensure only authorized users from trusted devices can access specific resources. Protect your users and your applications and get started on your zero trust access journey with Google Cloud today!
Resources
To learn more and see how you can set these up yourself, check out the following:
BeyondCorp EnterpriseAccess Context Manager overviewManaging access levelsThreat and Data protection for Chrome
Cloud BlogRead More