Snap Inc., creators of Snapchat, is a technology company that believes “the camera presents the greatest opportunity to improve the way people live and communicate.” Born in the cloud, Snap delivers its modern social media framework using Google Cloud.
In 2023, Google Cloud and Snap announced an expanded relationship that included Snap choosing Google Cloud for more workloads, including artificial intelligence, machine learning, and security services. One of the key aspects to securing these cloud workloads is a Zero Trust access framework, which became an essential part of Snap’s cloud journey.
“Beyond Corp Enterprise (BCE) is a focal component of our Corporate Security Program. As a born-in-the-cloud company, Snap has designed our program to allow for “Secure from Anywhere” access to Snap internal services largely without the need to use a VPN,” said Nick Reva, head of corporate security engineering at Snap. “Our partnership with Google to extend and integrate BCE with our internal services provides us with the mechanism to make access decisions based on device membership in corporate inventory and overall health. This is unparalleled capability provided by BCE, backed by the trust and security of Google Cloud”.
The “context” challenge
Snap decided to help address the challenge of securing their web applications by using Google Cloud’s BeyondCorp Enterprise (BCE). Snap’s security engineering team had previously designed an in-house HTTP reverse proxy, that provided authorization enforcement for all of their applications. In their pursuit to build a more durable and secure Zero Trust-based system, Snap needed granular device-context-based access control policies that could be configured for different user groups and different types of devices. However, Snap lacked a mechanism to collect and leverage device attributes for authorization.
BCE helps enable secure access to applications and resources anywhere in the world. It leverages Google’s global network infrastructure, enabling enterprises to deploy applications with global reach while minimizing worries about scaling and managing their network infrastructure.
It includes a robust device-attestation framework consisting of device attribute collection, context-aware access policy definitions, and a globally-deployed policy enforcement engine that enables modern Zero Trust network access control. One of the core components of BCE is the access proxy called Identity-Aware Proxy (IAP).
IAP supports user-based and programmatic access to resources and allows administrators to use custom claims in JSON Web Tokens (JWTs). Administrators can leverage this capability to forward additional information to the private application, enabling additional security and customization of their Zero Trust infrastructure.
A collaborative approach
Snap’s in-house HTTP proxy design supports multiple custom authentication methods that made it difficult for a wholesale migration from that to Google IAP. For example, one of Snap’s custom authentication methods known as Lightweight Client Auth (LCA) is an in-house solution that does not integrate with Google IAP today. Snap also ruled out incorporating other third-party authentication tools into IAP.
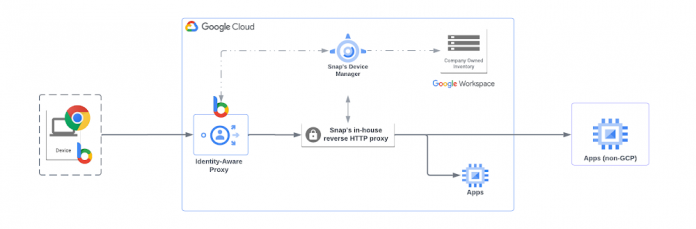
Google Cloud worked with Snap’s Production and Corporate Security Engineering teams to design an architecture that met Zero Trust standards and Snap’s requirements. While the approach was simple, to place IAP in front of their in-house HTTP proxy, the implementation was complex. IAP was configured to allow all users to access backend services. Once a user passes through IAP they are required to authenticate through Snap’s in-house HTTP proxy. BCE captures device attributes and IAP attaches this information to all requests, enriching requests sent to the in-house HTTP proxy.
A context-rich system for Zero Trust
IAP fronting requests to the in-house HTTP proxy gave Snap the ability to use the underlying features of BCE and leverage its existing internal enforcement engine. The new architecture allows IAP to associate a request with a device, its collected attributes, and associate these with a specific policy. This request is then proxied to the in-house HTTP proxy for policy evaluation and authorization. IAP passes all requests containing custom authentication transparently to the in-house HTTP proxy for enforcement, thus preserving critical custom authentication necessary for Snap’s backend services.
Snap relies on multiple in-house device inventory systems, some of which are internal and therefore not part of products offered by members of BeyondCorp Alliance that are already integrated with BCE. To keep the BCE device inventory up-to-date, the BCE APIs provide an alternate mechanism for integration. An in-house, custom-built service continuously keeps the BCE device inventory in sync with internal Snap inventories to add and prune devices as needed.
With Google Cloud’s help, Snap was able to lock down access to Snap’s internal services, which can now only be accessed from company-owned devices. Snap can apply access policies to the tens of thousands device objects in the new device inventory, as well as collect data from and gain visibility into thousands of corporate endpoints. Snap plans to expand use and leverage additional BCE functionalities such as Data Loss Prevention (DLP), malware and phishing prevention.
If you’d like to learn more about BeyondCorp Enterprise and Zero Trust access, check out our documentation. For details on how to leverage Identity-Aware Proxy, please visit our technical documentation.
Cloud BlogRead More