When thinking about modernizing an Oracle Database to an open-source database on AWS, options include Amazon Relational Database Service (Amazon RDS) for MySQL, Amazon RDS for MariaDB, Amazon RDS for PostgreSQL, or Amazon Aurora. The choice of target database is usually dependent on three major factors:
Database conversion or refactoring efforts
The enterprise-wide decision on choosing an open-source database engine
The desire to reduce operating costs, increase productivity, and improve employee and customer experience
After deciding on the target database engine, the next important step is to identify the database conversion and migration tool that will be best suited for the database migration. The most critical aspects of deciding a migration tool include its security compliance within the organization, its license requirements, and how it interacts with the source database.
AWS recommended tool for database conversion is AWS Schema Conversion Tool (AWS SCT). With this, you can convert tables, views, stored procedures, and functions to your desired target database engine. And AWS Database Migration Service (AWS DMS) is used for relational database migration to the AWS Cloud. The key features of using AWS DMS for database migration are security, minimal downtime, and its simple-to-use architecture.
The following AWS prescriptive guidance gives an overview to convert and migrate an on-premises Oracle database to an RDS for MySQL database using AWS DMS and AWS SCT. Additionally, the following migration playbook details the steps required to migrate from Oracle to an Aurora MySQL database, and can be used to migrate to any MySQL-compatible database, including MariaDB.
There could be various use cases where you would like to use Oracle GoldenGate (OGG) for migration. For example, if the source is a high transaction database, or when you need to do active-active replication between MySQL and Oracle. Another use case would be if OGG has already been approved by the organization’s security team or if you have already procured an OGG license and have expertise with it, or if you aren’t able to use AWS DMS. In such cases, using the AWS SCT for database conversion and OGG for database migration would make more sense.
In this post, we show you how to migrate an Oracle database to Amazon RDS for MySQL, Amazon RDS for MariaDB, or Amazon Aurora MySQL-Compatible Edition using OGG.
Solution overview
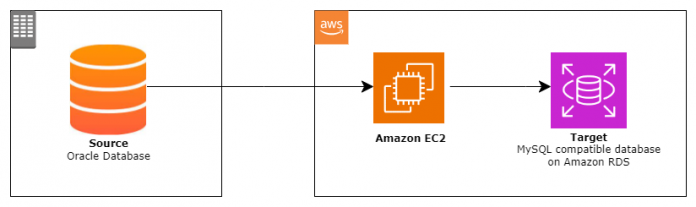
The following diagram shows the communication flow between your existing Oracle database—which could be on premises, on an Amazon Elastic Compute Cloud (Amazon EC2) instance, or Amazon RDS for Oracle), and the target MySQL compatible database.
The following figure provides more details on the individual components of OGG on Amazon EC2 to migrate an on-premises Oracle database to a MySQL-compatible database on Amazon Aurora or RDS.
A benefit of this solution is that you don’t have to move the trail files from one EC2 instance to another, which can improve migration performance. But there could be other ways of configuring this migration, such as using multiple EC2 instances, one with OGG for Oracle Libraries and a second with OGG for MySQL libraries. You could also install OGG for Oracle in an on-premises environment and OGG for MySQL on an EC2 instance in the same VPC as your target MySQL database.
In the following sections, we show how to set up the infrastructure and implement the solution.
Prerequisites
Before you use OGG to migrate the database, you must have the following:
A source Oracle database version 11 and above running on an existing on-premises environment, Oracle on Amazon EC2, or Amazon RDS for Oracle
Archive logging enabled on the source
A target MySQL version 5.7 and above or MariaDB version 10.4 and above database running on Amazon RDS or Aurora
An EC2 instance with the following:
An Oracle client
OGG for Oracle libraries
OGG for MySQL libraries
A database user account on both the source and target databases
Secure network connectivity between the EC2 instance with the source and target database server
Infrastructure setup
The following table details the environment and the database instance names used throughout this post.
Database role
IP address
Instance name
Database unique name
Database open mode
Database port
Source Oracle Database
172.31.xx.xx
ORASOURCE
orasource
Read write
1521
Target RDS for MySQL Database
172.31.xx.xx
mysqltest.xxxxx.ap-southeast-2.rds.amazonaws.com
testdb
Read write
1433
Amazon EC2 with with GoldenGate for Oracle and MySQL
172.31.xx.xx
–
–
–
–
Configure the source Oracle database
To configure the source Oracle database, complete the following steps:
Set the ENABLE_GOLDENGATE_REPLICATION parameter to True. This enables control services provided by the RDBMS for OGG.
Next, ensure supplemental logging is enabled at least at the database level:
In addition to minimum supplemental logging, it’s also recommended to put the Oracle database into forced logging mode. This makes sure that row chaining information is updated in the redo log for update operations.
Make sure that archive log retention is enabled. This is required to ensure OGG Replicat should be able to resume in case of any issues.
It’s always recommended to have a separate user for OGG with minimum privileges. The following command creates a database user with the minimum permissions that are required for OGG to work:
Additional permissions are required to query local metadata to generate the data definition file, which is used to convert database objects from Oracle to the MySQL engine:
Configure OGG for Oracle for initial load
Make sure OGG for Oracle on Amazon EC2 is able to connect to the source Oracle database. You can verify this by trying to connect from SQL*Plus or you can try connecting from the OGG for Oracle command line interface. Complete the following steps to configure OGG for Oracle for initial load:
Verify the source database connection.
Create subdirectories. The OGG configuration starts with creating the directory location for various files (listed in the following code) using the command Create subdirs:
The first and most important component of configuring OGG is the manager, which is required to run Extract and Replicat. This is a mandatory component to manage and run an OGG instance. As highlighted in solution overview, there will be a unique manager for OGG for Oracle and a separate manager process for OGG for MySQL. Use the following command to modify the content of the manager process:
The content of mgr.prm is as follows for Oracle:
After specifying the desired port for the manager for OGG for Oracle, you can start the manager. Make sure that port specified in the preceding file isn’t being used by any other process.
Optionally, you can create a wallet to store the source Oracle database credentials. With this approach, you just specify the alias and can avoid specifying user credentials in plain text in the Extract and Replicat configuration files.
After the wallet is created, edit the wallet with existing credentials:
When the wallet is ready, log in to the database from OGG for Oracle using the alias you created. You don’t need to specify database credentials again. You can use the dblogin utility:
The next step is to run the DEFGEN utility, which generates a file with field descriptions for each column entry of tables or schemas listed in the defgen parameter file. To modify the schema name and file output location, you must modify the parameter file for the defgen utility:
The content of defgen.prm looks like the following code. It generates a structure of all tables in the DMS_SAMPLE schema. We have used DMS_SAMPLE as the sample schema for the source database. You can modify this based on your schema name or only tables that you are planning to convert and migrate to MySQL.
After you create the parameter file for defgen with the correct user credentials and a list of tables and schemas to be migrated, you can run it as follows:
The defgen utility creates a sample file like the following example, containing information regarding all the tables. This file size could vary based on the number of tables mentioned in the parameter file. The file is used to translate the Oracle data to MySQL data.
After you generate the file, copy it to the corresponding directory on OGG for MySQL. In our solution, we use just one EC2 instance for the individual installation for OGG for Oracle (location: /u01/app/oracle/product/gg_src) and OGG for MySQL (location: /u01/app/oracle/product/gg_trg):
Enable unconditional logging of the primary key and the conditional supplemental logging of all unique keys and foreign keys of all tables on the source Oracle database:
This isn’t required if you just have to load data one time (you won’t be using OGG to replicate ongoing changes).
Schematrandata adds the supplemental logging and records the SCN (Oracle System Change Number). This allows for a second Replicat process (for CDC only) to start applying the changes from the point where the initial load extract stopped. Therefore, it’s mandatory to enable this before starting the first extract to load initial data.
If you want supplemental logging to be enabled independent to OGG, you have to add supplemental logging using the following commands on each table:
Adding schematrandata is still required to keep track of the SCN for ongoing replication changes. Another option would be to keep track of the SCN and start the second Replicat process (for CDC) using the SCN that was recorded before the start of first extract process (for initial load).
The output of adding schematrandata on all tables in the schema looks like the following code:
Configuring Extract is the next step, which runs against the source Oracle database and is used for the initial data load. The parameter SOURCEISTABLE defines that Extract pulls a static dataset from the source database without using any checkpoint information. Information regarding this Extract isn’t visible with the info all command, but you can use the following command to identify the current status:
This is followed by another Extract (as explain in the solution overview), which is used separately to replicate ongoing changes.
You can add the initial Extract using the following command:
The content of the initial load Extract looks like the following code. In this extract, we are planning to migrate all tables under the schema DMS_SAMPLE. You can replace the schema names with your desired schema to be migrated or just list of tables that will be involved in migration.
Configure OGG for MySQL for initial load
This process is similar to creating subdirectories for OGG for Oracle. Because OGG for MySQL is on the same instance, we need to make sure the directory selected to create subdirectories is different from OGG for Oracle.
Create subdirectories with the following code:
A separate manager process for OGG for MySQL is required. This needs to be configured to be run on a different port to avoid conflict with the port in use for OGG for Oracle:
The content of mgr.prm for MySQL is as follows:
Start the manager for OGG for MySQL:
At this stage, there are two OGG managers running on the same machine.
Make sure the database is available on the target MySQL database. The target database name could be anything and doesn’t necessarily need to be the same as the source database. Also, tables that you are planning to migrate should already exist. If you are unsure how to convert Oracle tables into a MySQL-compatible database, you can use AWS SCT. For instructions, refer to Use the AWS Schema Conversion Tool to Convert the Oracle Schema to Aurora MySQL.
Create database on the target MySQL instance:
You can verify the connection to the target MySQL database is successful by using the DBLOGIN utility and specifying the endpoint of your target MySQL database. This could be Amazon RDS for MySQL, Amazon RDS for MariaDB, or Aurora MySQL-Compatible. If Aurora MySQL-Compatible is the target, make sure to use the cluster endpoint to connect to the Aurora MySQL writer instance.
Verify the connection to the target MySQL from OGG for MySQL:
Configure the Replicat process in OGG for MySQL. The Replicat process is responsible for migrating data to the target database. The parameter SPECIALRUN highlights that this Replicat is used only for the initial load process:
Because this Replicat is only for the initial load, its status won’t be visible in the standard info all command from OGG for MySQL. Instead, use the following code:
You can modify the contents of Replicat using the following command from OGG for MySQL:
The contents of the Replicat process look like the following code. You need to specify the SOURCEDEFS file that was generated earlier using the DEFGEN utility:
It’s important to understand that default tables in Oracle are created in uppercase, whereas tables in MySQL by default are created in lowercase. In the preceding scenario, while specifying * for target tables, you need to make sure all tables in the target MySQL database are also created in uppercase (the same as Oracle). However, the right approach would be to create tables in the target MySQL database in lowercase and specify table mapping separately for all tables. The Replicat configuration file looks like the following code:
Disable foreign key constraints before initial load
Foreign key constraints on the target MySQL must be disabled before starting the initial load. This can be done by modifying the RDS parameter init_connect as ‘SET FOREIGN_KEY_CHECKS=0’. It’s a dynamic parameter and will be applied without database restart. Setting this parameter disables foreign key checks for all DML commands. When the initial load is complete, you must enable it again before the extract for ongoing replication is started.
Run the initial data load
Complete the following steps to run the initial data load:
Connect to OGG for Oracle GGSCI and check the status of the manager and Extract using info all. This won’t give you the information for the SPECIALRUN Extract and will only show the status of the manager:
When all the configuration of the initial load Extract and Replicat is complete, start the Extract to perform the initial database migration:
Verify the status of Extract with the following command from OGG for Oracle:
The output looks like the following for the Extract process (on OGG for Oracle):
Similarly, the status of the Replicat process can be identified as follows (on OGG for MySQL):
The output looks like the following code:
If you are not able to see the data on target table, check ggserr.log under /u01/app/oracle/product/gg_src/ for Extract errors and /u01/app/oracle/product/gg_trg/ for Replicat error messages. Similarly, if Extract or Replicat is in an abended state, look for ggserr.log in the respective folder to identify the root cause.
Configure OGG for Oracle for ongoing replication changes
This section covers settings to configure ongoing replication changes. To modify parameters that relate to the OGG for Oracle instance as a whole, you have to update the GLOBALS file. If there any parameters that you want to apply to all extracts, you can add them here. Complete the following steps:
Edit the GLOBALS parameter in OGG for Oracle:
Update the parameter ALLOWOUTPUTDIR to specify the allowed output trail directory (which must already exist):
It’s required to register the primary extract group with an Oracle database for enabling integrated capture mode:
The benefit of integrated capture mode is that the Extract process interacts directly with the database log mining server, whereas in the case of classic capture mode, changes need to read from Oracle redo or archive log files. Another benefit of having integrated capture mode is it supports more data and storage types compared to classic capture mode.
Create an extract group in integrated mode:
The Extract parameter file needs to be updated with the host details and port number where the OGG for MySQL libraries are configured. In our case, both (Oracle and MySQL) are configured on one single host but different ports, therefore we specify 7810, which is for OGG for MySQL. Tables that you would like OGG to replicate must be specified here. You have the option to specify * to replicate all tables or you could only specify tables that are continuously updating and leave the static tables to be migrated using the initial extract.
Use the following code:
When Oracle Automatic Storage Management (ASM) is in use, the TRANLOGOPTIONS ASMUSER and ASMPASSWORD must be set in the Extract parameter file.
At this stage, the process on OGG for Oracle looks like the following code:
The next step is to add RMTTRAIL and specify the exact same location for the remote trail while creating the extract to replicate ongoing changes:
Configure OGG for MySQL for ongoing replication changes
To configure OGG for MySQL to replicate ongoing changes to the MySQL database, complete the following steps:
Log in to the target MySQL from OGG for MySQL:
You need to update the parameter ALLOWOUTPUTDIR in the GLOBALS file, similar to what we did for OGG for Oracle, to specify the allowed output trail directory (which must already exist):
The GLOBALS file looks like the following code:
Make sure there is no table with the same name in target database that is mentioned in GLOBALS parameter file.
The next step is to configure the Replicat at OGG for MySQL. Because we specified the manager port of OGG for MySQL in the extract created in OGG for Oracle, this integrates with the extract that was created in OGG for Oracle:
You must specify the SOURCEDEFS file, which was previously generated and used for the Extract for the initial load. The discard file holds information regarding the operations that failed while applying changes to the target database. Additionally, mapping (as explained earlier) needs to take care of Oracle uppercase and MySQL lowercase. If you specify * to replicate all tables, MySQL must have all tables created in uppercase as well. HANDLECOLLISIONS is an important parameter that takes care of duplicates and ensures no records are missed from migration.
Use the following code:
Use CHECKPOINTTABLE to create a checkpoint table with the name that was specified in the GLOBALS parameter file. It’s important to specify the checkpoint table, which records the read position and is helpful to resume the Replicat from the point where it was last stopped or failed.
The last step is to add the Replicat with the EXTTRAIL, which is the same as the RMTTRAIL created for the earlier Extract process:
At this stage, the process on OGG for MySQL looks like the following code:
Enable foreign key constraints before ongoing replication changes
The same parameter init_connect is modified to the value ‘SET FOREIGN_KEY_CHECKS=0’. This makes sure that data replicated from the source is consistent on the target and doesn’t encounter any integrity constraint violations.
Start ongoing replication changes
The final step is to start the extract first to start capturing changes from the source database.
Run the following code in OGG for Oracle GGSCI:
Then you start the Replicat process, which starts applying changes to the target database:
At this stage, OGG starts replicating any changes happening in your source Oracle database to the target database. You can verify by performing some DMLs (inserts, updates, and deletes) to see if they are being replicated correctly to the target database.
Verify the status of rmttrail by looking at the info rmttrail command:
To verify the status of Extract (for ongoing replication changes), you can look at the info command on OGG for Oracle. This command also provides the checkpoint information and the process run history:
The view report command provides more information about the discard file generated by Extract:
Similarly, you can view the status and information for Replicat on OGG for MySQL:
Clean up
To avoid incurring future charges, delete the EC2 instance on which OGG for Oracle and OGG for MySQL were installed.
On the Amazon EC2 console, navigate to the Instances page, select the instance, and then choose Terminate instance on the Instance state menu.
Summary
In this post, we discussed how to migrate between an Oracle database to a MySQL-compatible database using OGG. We also looked into the configuration steps to continuously replicate ongoing changes from an Oracle database to a MySQL-compatible database.
Try these settings in your next Oracle database migration to a MySQL-compatible database. If you have any comments or questions, leave them in the comments section.
About the Authors
Viqash Adwani is a Sr. Database Specialty Architect with Amazon Web Services. He works with internal and external Amazon customers to build secure, scalable, and resilient architectures in the AWS Cloud and help customers perform migrations from on-premises databases to Amazon RDS and Amazon Aurora databases.
Subhash Raut is a Database Migration Specialist Solutions Architect at AWS. He works on challenges related to database migrations and works closely with customers to help them realize the true potential of AWS DB migration tools.
Dilip Sasikumar is a Technical Account Manager with Amazon Web Services and is based in Melbourne, Australia. He works with enterprise support customers providing assistance on operational excellence, cost optimization and security. Dilip is also a database enthusiast with keen interest in relational databases and database migrations.
Read MoreAWS Database Blog