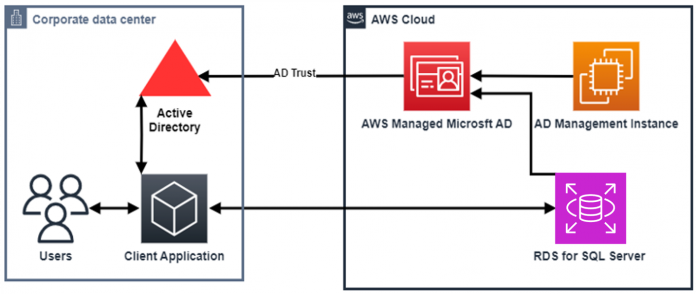
In this post, we show you how to integrate your Amazon Relational Database Service (Amazon RDS) for SQL Server instances with your self-managed Active Directory (AD). Previously, you could only join your RDS for SQL Server instances to an AWS Managed Microsoft AD directory. You were able to connect your on-premises AD via a trust relationship between an AWS Managed Microsoft AD and your on-premises AD, as shown in the following figure.
With the launch of self-managed Active Directory support, you can join your RDS for SQL Server instances directly to your self-managed AD domains regardless of where it is hosted. Your AD can be hosted in your corporate data centers, on Amazon Elastic Compute Cloud (Amazon EC2), or other cloud providers. The following diagram shows the scenario when joining to a self-managed AD.AWS Direct Connect or VPN can be configured for the traffic between the corporate environment and the VPC.
Solution overview
To implement RDS for SQL Server instances with self-managed Active Directory, you first need to create 3 objects in Active Directory:
An Organizational Unit (OU) for the Amazon RDS for SQL Server deployment
An AD service account for the Amazon RDS for SQL Server deployments and management
Delegate the AD service account with limited permissions to the OU
We recommend creating a new OU and AD service account for each RDS for SQL Server instance deployment. Doing so increases your security boundary.
The following diagram illustrates the solution architecture.
To simplify the setup of the AD objects, we created a PowerShell script to create the objects and set the appropriate permissions for you. The script can be downloaded here.
In the following sections, we discuss the steps to create an AD OU and an AD service account, and create an AWS Key Management Service (AWS KMS) key and secret in AWS Secrets Manager to store your Amazon RDS AD service account credentials.
First, you create the AD objects required to integrate Amazon RDS for SQL Server with a self-managed Microsoft AD. You use a PowerShell script to generate all of the prerequisites prior to deploying Amazon RDS for SQL Server. Specifically, the script creates the following:
An OU for Amazon RDS for SQL Server named RDS-MSSQL (or any name of your choice)
An AD service account for Amazon RDS for SQL Server named RdsServiceAccount (or any name of your choice) with the proper least-privilege permissions
Next, you create a new Secrets Manager secret to store your service account information and a new KMS key to encrypt the secret. After you have stored the service account information, you update the secret’s resource permission, granting the Amazon RDS service principal GetSecretValue permissions.
Lastly, you create an RDS subnet group, deploy your RDS for SQL Server instance integrated with your self-managed AD, and validate the deployment.
Pricing estimate for resources deployed in this post
If you plan on using your own directory, make sure you use the information for your environment.
The estimated total cost to run the resources for 24 hours is $29.54 (USD) in the us-west-2 region. The following table summarizes the pricing details.
Service
Count
Price per Hour (USD)
Region
Estimated 24 Hour Cost (USD)
Calculations
Secrets Manager secret
2
$0.00056
us-west-2
$0.03
= 0.00056 * 2 * 24
t3.large EC2 Windows instance
1
$0.1108
us-west-2
$2.66
= 0.1108 *24
t3.medium EC2 Windows instance
1
$0.06
us-west-2
$1.44
= 0.06 * 24
Amazon EBS General Purpose SSD (gp3) – storage
90
$0.08 GB-Month
us-west-2
$0.24
= .08 * 90 * 86400 / 2,592,000
KMS service key
1
$0.0014
us-west-2
$0.03
= 0.0014 * 24
Amazon RDS for SQL Server Standard (single AZ – db.t3.xlarge)
1
$1.044
us-west-2
$25.06
= 1.044 *24
Amazon RDS database storage (General Purpose (SSD) storage)
20
$0.115 GB-Month
us-west-2
$0.08
= .115 * 20 * 86400 / 2,592,000
Prerequisites
You need the following resources deployed to follow along with this post:
An Active Directory, either self-managed or using AWS Managed Microsoft AD. Both work with the implementation steps. For this post, we use a single domain controller self-managed AD with the domain name of corp.example.com. Note that this post uses a bootstrapped self-managed AD on an EC2 instances and should not be used for production purposes. If you are using a different domain name, make sure you update it where appropriate.
An EC2 Windows Server instance (referred to as the MGMT EC2 instance in this post) joined to your AD with the Active Directory Administration tool and SQL Server Management Studio (SSMS) installed.
We provide an AWS CloudFormation template to help you deploy the prerequisites in a new VPC. The template can be downloaded here.
Deploy the CloudFormation template
To deploy the CloudFormation template, complete the following steps:
On the AWS CloudFormation console, choose Create stack.
Select Upload a template file, then choose Choose file.
Browse to the CloudFormation template you downloaded, then choose Next.
For Stack name, enter RDS-Self-AD.
In the Parameters section, leave the defaults.
On the Configure stack options page, leave the defaults and choose Next.
On the Review stack page, select I acknowledge that AWS CloudFormation might create IAM resources with custom names and choose Submit.
Create the Active Directory OU and service account
To set up your Active Directory OU and service account, complete the following steps:
On the Secrets Manager console, navigate to the OnPremAdministratorSecret secret.
Under Secret details, choose Retrieve secret value.
Note the key-value for the password to use later.
Open the AWS Systems Manager Fleet Manager Remote Desktop console.
Choose Add new session, then select the MGMT EC2 instance node and choose Add.
Select User credentials and enter the following.
For Username, enter corpAdministrator.
For Password, enter the value you retrieved from the OnPremAdministratorSecret secret.
Choose Connect.
Download the PowerShell script here that creates the OU and service account.
Choose (right-click) Start and select Windows PowerShell (Admin).
In the Windows PowerShell window, make sure you are in the directory you downloaded the script to and run the following code (if you’re deploying this in your own environment, update the $RDSDeployment hash table variable with the proper values).
The script output should look like the following:
Create a KMS key and secret to store the Amazon RDS service account credentials
Now that you have created the target OU and service account with proper delegation, you need to store the service account information in a Secrets Manager secret.
Set up the KMS key
To configure your KMS key, complete the following steps:
On the AWS KMS console, choose Customer managed keys in the navigation pane.
Choose Create key.
For Key type, select Symmetric.
For Key usage, select Encrypt and decrypt.
In the Advanced options section, for Key material origin, select KMS.
For Regionality, select Single-Region key.
Choose Next.
On the Add labels page, enter an alias (for this post, we enter RDS-Self-AD), then choose Next.
On the Define key administrative permissions page, select your IAM user or role, then choose Next.
On the Define key usage permissions page, select your IAM user or role, then choose Next.
On the Review page, review your selections and choose Finish.
On the AWS KMS console, choose the alias of the key you just created.
On the Key policy tab, select Switch to policy view, then choose Edit.
Append the following to your key policy and choose Save changes:
Note: For Encryption Key, don’t use the AWS default KMS key. Be sure to create the AWS KMS key in the same AWS account that contains the RDS for SQL Server DB instance that you want to join to your self-managed AD
Store the service account credentials in a Secrets Manager secret
To store your credentials in a Secrets Manager secret, complete the following steps.
On the Secrets Manager console, choose Store a new secret.
For Secret type, select Other type of secret.
For Key/value pairs, add the following key pair.
For the key, enter CUSTOMER_MANAGED_ACTIVE_DIRECTORY_USERNAME.
For the value, enter the name you passed in the RdsSvcAccountName parameter of the PowerShell script.
Choose Add row and add another key pair.
For the key, enter CUSTOMER_MANAGED_ACTIVE_DIRECTORY_PASSWORD.
For the value, enter the password you passed for the RdsSvcAccountPw parameter of the PowerShell script.
For Encryption key, choose the key you created earlier.
Choose Next.
For Secret name, enter a name (for this post, we use RDS-Self).
In the Resource permissions section, choose Edit permissions.
Enter the following resource policy, then choose Save:
Note: The AWS account IDs used in this blog are for demonstration only. Readers should change the AWS account IDs accordingly.
On the Configure rotation page, leave the defaults and choose Next.
On the Review page, review your selections and choose Store.
On the Secrets Manager console, choose the refresh icon and choose the secret name you just created.
On the Secret details page, make note of the secret ARN to use when you deploy the RDS for SQL instance.
Create an RDS subnet group
In this step, you create a DB subnet group. A DB subnet group is a collection of subnets in a VPC that you then designate for your DB instances. Each DB subnet group should have subnets in at least two Availability Zones in a given Region. When creating a DB instance in a VPC, you choose a DB subnet group for it. From the DB subnet group, Amazon RDS chooses a subnet and an IP address within that subnet to associate with the DB instance. The DB uses the Availability Zone that contains the subnet.
On the Amazon RDS console, choose Subnet groups in the navigation pane.
Choose Create DB subnet group.
For Name, enter a name (for this post, we enter RDS-Self-AD).
For Description, enter a description (for this post, we enter RDS-Self-AD).
For VPC, choose the VPC that contains the subnets you wish to deploy your RDS instance to.
For Availability Zones, choose the Availability Zones containing the subnets you wish to deploy your RDS instance to.
For Subnets, choose the subnets you wish to deploy your RDS instance to.
Choose Create.
Deploy the RDS for SQL instance integrated with the self-managed AD
In this step, you deploy the RDS for SQL Server instance and join it to your self-managed AD. We don’t walk you through the whole process of deploying an RDS for SQL Server instance; we only point out the configuration settings needed to join RDS for SQL Server instances to AD. For full deployment instructions, refer to Creating an DB instance.
On the Amazon RDS console, choose Databases in the navigation pane.
Choose Create database.
Select Enable Microsoft SQL Server Windows authentication.
For Windows authentication type, select External Active Directory Domain.
For Fully qualified domain name, enter the name of the domain your RDS instance will use (for this post, we use corp.example.com).
For Domain organizational unit, enter the location for your Amazon RDS AD objects (for this post, we enter OU=RDS-MSSQL,DC=corp,DC=example,DC=com).
For Authorization secret ARN, enter the ARN of the secret containing the service account credentials you created.
For Primary DNS, enter a DNS resolver IP of the DNS service that can resolve your self-managed AD.
For Secondary DNS, enter a DNS resolver IP of the DNS service that can resolve your self-managed AD.
Validate all your other settings.
Validate deployment
When your RDS for SQL Server instance is active, you can connect to the instances from the MGMT EC2 instance node using SSMS with the local service account credentials you set when you deployed the instance. Once logged in, you give the corpAdministrator account permission to authenticate into the RDS for SQL Server instance. Complete the following steps:
On the Secrets Manager console, navigate to the secret OnPremAdministratorSecret.
On the Secret details page, in the Secret value section, choose Retrieve secret value.
Note the password for the corpAdministrator account to use in later steps.
Open the AWS Systems Manager Fleet Manager Remote Desktop console.
Choose Add new session, select the MGMT EC2 instance node, and choose Add.
Select User credentials and enter the following:
For Username, enter corpAdministrator.
For Password, enter the password you copied for the OnPremAdministratorSecret secret.
Choose Connect.
Choose Start and launch SSMS.
In the dialog box, provide the following information:
For Server name, enter the name of the RDS for SQL Server instance endpoint.
For Authentication, choose SQL Server Authentication.
For Login, enter the user name you set when you launched the directory.
For Password, enter the password you set when you launched the directory.
Choose Connect.
Once in SSMS, in the navigation pane, expand Security and Logins.
Choose (right-click) Logins and choose New Login.
Enter corpAdministrator for the login name and choose OK.
Choose Start and open a new SSMS window.
In the dialog box, provide the following information:
For Server name, enter the name of the RDS for SQL Server instance endpoint.
For Authentication, choose Windows Authentication.
Choose Connect.
Congratulations! You have successfully signed in to your RDS for SQL Server instance with a user from your self-managed Active Directory.
Clean up
To remove the resources deployed in your account from this post, complete the following steps:
Delete the RDS for SQL Server instance you deployed for this post. For instructions, refer to Deleting a DB instance.
Delete the RDS-Self-AD secret you created. For instructions, refer to Delete an AWS Secrets Manager secret.
Delete the RDS-Self-AD key you created. For instructions, refer to Deleting AWS KMS keys.
Delete the CloudFormation stack that deployed all the prerequisites for this post. For instructions, refer to Deleting a stack on the AWS CloudFormation console.
Summary
In this post, we showed how to deploy an RDS for SQL Server instance integrated with a self-managed AD. We used a sample PowerShell script that easily set up all the Active Directory prerequisites for this new capability. Next, we created a KMS key to encrypt a Secrets Manager secret containing the Amazon RDS AD service account credentials, and deployed a new RDS for SQL Server instance integrated with a self-managed Microsoft AD. Finally, we showed how to validate a self-managed Microsoft AD user to authenticate into the RDS for SQL instance.
Keep an eye out for future posts on this new and exciting capability. if you have any questions or comments please add them below.
About the Authors
Jeremy Girven is a solutions architect specializing in Microsoft workloads on AWS. He has over 17 years’ experience with Microsoft Active Directory and over 25 years of industry experience. One of his fun projects is using SSMS to automate the Active Directory build processes in AWS. To see more, check out the Active Directory AWS Partner Solution.
Siva Thang is a Senior Solutions Architect, Partners with AWS. His specialty is in databases and analytics, and he also holds a master’s degree in Engineering. Siva is deeply passionate about helping customers build a modern data platform in the cloud that includes migrating to modern relational databases and building data lakes and data pipelines at scale for analytics and machine learning. Siva also likes to present in various conferences and summits on the topic of modern databases and analytics.
Pradipta Kishore Das has vast experience in database management systems and has over 18 years of experience with Microsoft SQL Server. He is currently working as a Database Engineer with Amazon Web Services. He works with the Amazon RDS team in building new and exciting features for customers, focusing on commercial database engines and SQL Server. In the past, he was a Technical Lead at Microsoft, which involved troubleshooting complex SQL Server issues and debugging. He has worked on environments of various scales.
Read MoreAWS Database Blog