Ethereum is a decentralized, open-source blockchain with smart contract functionality. The Beacon chain (ETH2) is an upgrade to Ethereum that introduced a proof-of-stake concept to the Ethereum ecosystem. Staking in ETH2 is done by validators who perform actions such as attestations and block proposal activities to improve the Ethereum network’s security and scalability. Validators in turn are rewarded for the staking actions they perform.
AWS currently offers the Amazon Managed Blockchain (AMB) which is a fully managed service that makes it easy to create and manage scalable blockchain networks using popular open source frameworks. Today we support Hyperledger Fabric private permissioned networks, and Ethereum full nodes that connect to the public mainnet and two popular testnets, Rinkeby and Ropsten. Amazon Managed Blockchain does not currently support the Ethereum Beacon chain at present.
Rocket Pool is one of many decentralized staking pools that supports the Beacon chain. Validators who wish to earn rewards for staking may use Rocket Pool to create their own validation nodes. These validation nodes may be run on Amazon Elastic Compute Cloud (Amazon EC2) powered by Graviton2 processors. In this post, we introduce an AWS Cloud Development Kit (AWS CDK) app that simplifies the deployment of Rocket Pool on Amazon EC2.
Solution overview
CDK is is an open-source software development framework that defines cloud application resources using familiar programming languages.
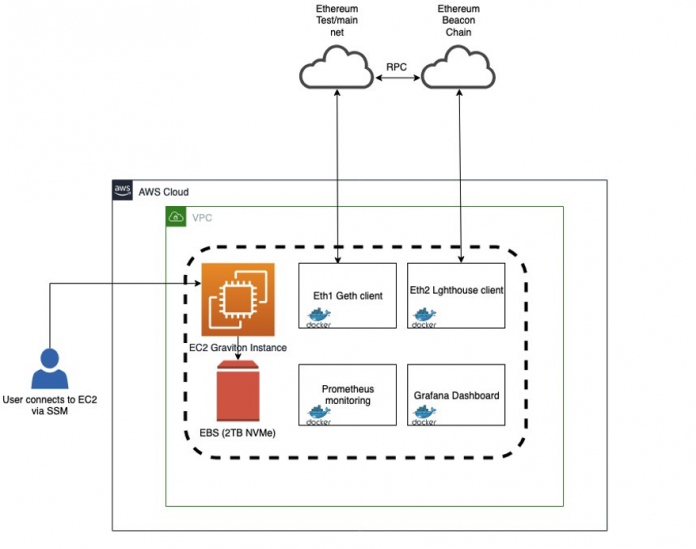
Our CDK app creates a Rocket Pool validation node using a c6g.2xlarge instance containing 8 vCPUs and 16 GB of memory. The c6g instances are powered by Graviton2 processors and are ideal for blockchain workloads like Ethereum validation. We also configure a 2 TB Amazon Elastic Block Store (EBS) device for high-performance block-storage and AWS Systems Manager Session Manager for secure access.
The following diagram illustrates the process for initializing, synthesizing, and deploying your app using AWS CDK.
Our deployment performs validation for both ETH1 and ETH2 blockchain networks. By default, this node is configured to use the Geth client for ETH1 validation and the Lighthouse client for ETH2 validation. You can modify these client configurations using the Rocket Pool CLI after deployment.
You can use AWS CDK on your local desktop. Follow these instructions to get started with AWS CDK.
Download and install the dependencies and the Rocket Pool AWS CDK application
Use the following code to download and install the dependencies and the AWS CDK app:
Rocket Pool recommends deploying a node with 16 GB or 32 GB memory. For this post, we deployed with a 16 GB instance. However, if you want to increase the memory, you can modify the lib/cdk-rocketpool-validator-stack.ts file. For example, in the following deployment code, change ec2.InstanceSize.XLARGE2 to ec2.InstanceSize.XLARGE3 or XLARGE4:
When the deployment is complete, you get the following output:
At this point, run the sshcommand from the AWS CDK Outputs to log in to your instance:
The following is your sample output:
Completing the installation
Once you are connected you can run the following command to complete the rest of the installation.
(Optional) If at any point you want to change your ETH1/ ETH2 clients you can run the following command. The default client for ETH1 is Geth and for ETH2 is Lighthouse.
For more information, refer to Configuring the Smartnode Stack. The preceding stack was implemented on the Prater test network. If you want to switch it to the mainnet, refer to Pool Staking on Mainnet.
Rocket pool comes with support for Grafana and has a pre-built dashboard for each of the ETH2 clients. You can login to Grafana by navigating your browser to http://<your node IP>:<grafana port>. The Grafana port is configured to be 3100 by default. You may find additional information including default login credentials and instructions for importing dashboards in the Setting up Grafana section of the Rocket Pool documentation. Below is a sample image of the dashboard displaying metrics for a Prysm ETH2 client.
Clean up
Clean up the resources from this post with the following code:
Conclusion
Rocket Pool enables Ethereum node validators to earn rewards through proof-of-staking. In this post, we showed you how to deploy an ETH2 validator on Rocket Pool in the AWS Cloud with minimal setup time using AWS CDK. We also demonstrated how to access your node securely using Session Manager. We encourage to try it out on the testnet before you deploy your ETH validator on the mainnet.
If you’d like to leave feedback or have additional questions, we invite you to leave a comment.
About the Authors
Raj Seshadri is a Global SA Lead with AWS and is a member of the containers Technical Field Community. He is passionate about blockchain technology including Ethereum, Web3, NFT and Defi. Prior to AWS, he had stints at Aqua Security, Red Hat, Dell and EMC. In his spare time, he plays tennis and enjoys traveling around the world. You can reach him on Twitter @texanraj.
Dan Fox is a Principal Specialist Solutions Architect in the Worldwide Specialist Organization for Serverless. Dan works with customers to help them leverage serverless services to build applications that are scalable, fault-tolerant, high-performing, secure, and cost-effective. Dan is grateful to be able to live and work in lovely Boulder, Colorado.
Charles Okochu is the Global Business Development Manager for Amazon Managed Blockchain and Amazon Quantum Ledger Database (QLDB). He is based out of New York City and has a background in Financial Services, Blockchain, Digital Assets and is passionate about how blockchain technologies can transform the technology landscape. In his spare time, Charles enjoys running, playing and coaching soccer, and spending time with friends and family.
Read MoreAWS Database Blog