Google Cloud Firewall is a fully distributed, stateful inspection firewall engine that is built into our software-defined networking fabric and enforced at each workload. With Cloud Firewall, you can enhance and simplify security posture, and implement Zero Trust networking for cloud workloads.
Previously, we announced several enhancements and expansions to our Cloud Firewall offering. Today, we are excited to announce the general availability for the following Cloud Firewall features:
Threat Intelligence for Cloud Firewall: curated threat intelligence lists built and maintained by Google
Geo-location objects: filter traffic based on specific geographic locations
Address groups: user-defined collection of IPs or IP ranges
Local IP ranges: granular control for target workloads
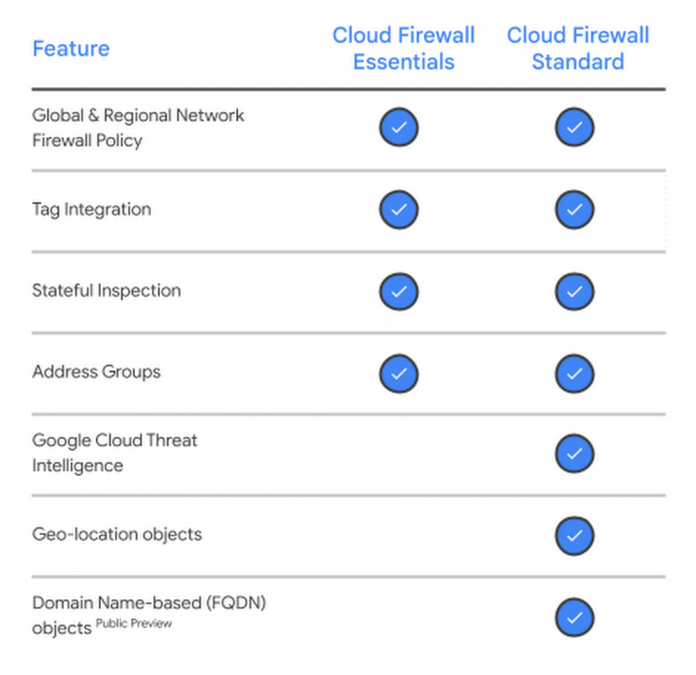
These features are available in two tiers shown in the graphic below: Essentials, the foundational set of capabilities; and Standard, which expands rule capabilities. These features can now be activated through the Cloud Console, Command Line Interface, and API.
Threat Intelligence for Cloud Firewall
Threat Intelligence for Cloud Firewall can help identify and block malicious traffic or allow known good traffic for your cloud workloads. This feature allows you to enhance your firewall rules with curated lists of threat intelligence data from a combination of Google, third-party, and open source databases. These lists are maintained and constantly updated by Google Cloud Threat Intelligence researchers to help keep your firewall rules up-to-date.
For example, you can use Threat Intelligence for Cloud Firewall to block known malicious IP addresses to help prevent attackers from reaching your network, or allow good traffic from trusted sources such as search engine crawlers.
Geo-location objects
IP address ranges are constantly changing around the globe. The introduction of geo-location objects can allow you to block traffic from designated geographic locations, even as the underlying IPs change. Google builds and maintains the country to IP address mapping for you, helping you reduce cost and effort to maintain this information. This helps enable you to enforce compliance with regulations by blocking traffic from certain locations.
Address groups
Address groups can help you simplify setting and maintaining your firewall rules. Creating multiple rules that reference the same set of source and/or destination IPs is a common firewall management task. Previously, users needed to separately maintain these IP range sets and manually enter these IP ranges in each rule that references them.
Address groups are a collection of IPs or IP range sets. With address groups, you can maintain your own address group at either project or organization level, reuse the same object in multiple different firewall rules, and use it in the new network firewall policies. This can save you time and effort to manage firewall rules, ensure consistency, and it can also help to reduce errors by making it easier to understand and troubleshoot your firewall configuration.
Local IP ranges
For firewall rule configurations, you may specify the target tag or service account for a rule to be applied. If there is a tag or service account in the firewall rule configuration, then only workloads with the specific tag or service account will be impacted by the rule. Previously, if you specified a tag or service account, then you were unable to further use an IP address of a target workload. For example, if the target workload is a GKE node with multiple IPs assigned to it, then the previous configuration did not enable you to only allow traffic from a particular IP.
We are excited to announce the general availability oflocal IP ranges for Cloud Firewall. With local IP range support, you can configure destination IPs in ingress firewall rules to allow ingress traffic targeting for only a specific IP for the virtual machine (VM) interface. Local IP ranges are available in both source and destination IP ranges in ingress and egress rules, which enables traffic filtering through a gateway style endpoint. You can achieve this by configuring symmetrical firewall rules that include a destination IP for an ingress rule, and source IP for an egress rule.
Forrester Wave™ IaaS Platform Native Security
These offerings were evaluated as part of The Forrester Wave™: Infrastructure-As-A-Service Platform Native Security for Q2 2023, where Google was named a Leader. In the Wave, Forrester evaluated the cloud-first security capabilities and go-to-market of the most significant cloud platform providers based on each vendor’s Current Offering, Strategy, and Market Presence. Of the eight vendors, Google Cloud received the highest score in the Strategy category, and received the most 5 out of 5 ratings across the 22 criteria evaluated in the Wave.
The report states that, “Google offers convincing admin IAM capabilities, and robust hypervisor and confidential computing security. Network security, especially web application firewall and segmentation/microsegmentation, are ahead of competitors.” Read more about the report here.
Take the next step
Cloud Firewall can help you move toward a Zero Trust network posture for cloud workloads using a scalable, cloud-first, stateful inspection firewall service with advanced protection capabilities. With a fully distributed architecture, Cloud Firewall can enable micro-segmentation through granular controls enforced at the VM level. The latest updates to Cloud Firewall Standard, now available in GA, provides additional capabilities to simplify firewall management to help protect your cloud workloads.
To learn more, check out the documentation here to activate the features in your cloud environment or get started in the cloud console here.
Cloud BlogRead More